 How hijackable is your domain?
How hijackable is your domain? What are the top issues involving your digital assets?
What are the top issues involving your digital assets? Are there exposed cloud storage or web interfaces?
Are there exposed cloud storage or web interfaces? Think your digital assets are secure? Think again!
Think your digital assets are secure? Think again!
Cyberint's attack surface analysis reveals all and will help you prioritize your efforts in lowering digital risk.
Our assessment process starts by mapping your company’s digital presence. It's followed by non-intrusive detection and analysis of threats, access points, compromised credentials, exploitations and misconfigurations.
Your domain will then be given a security score by assessing the findings of our analysis in the face of current threats and security best practices.
Get your personalized domain analysis now:
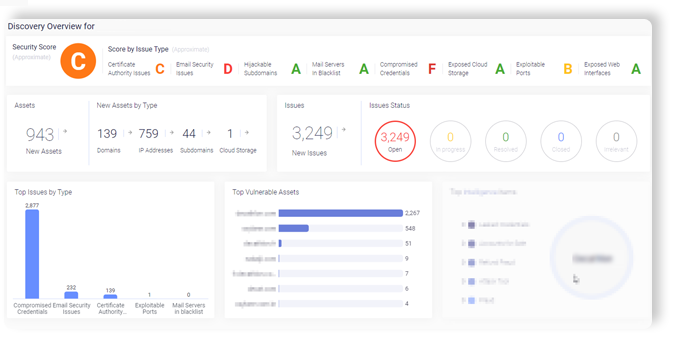
Example attack surface monitoring results
Knowing how vulnerable your attack surface has never been more important. In 2020 cyber attacks grew significantly and they’re not forecast to slow down in 2021.
Our amo will highlight your weak spots, allowing you to get an immediate attack surface management plan to mitigate risk and improve security posture.
Analyze my domain now
We will share with you a snapshot in time of your attack surface initial analysis. A full discovery will be done at onboarding.
Cyberint uses a wide range of sources to increase accuracy to make our attack surface tools highly accurate.
Your attack surface changes frequently. A one-time shot is helpful in highlighting issues, but for ongoing issues, ongoing alerts are necessary.
When you are a Cyberint customer you get the full report and the ability to rescan over time according to intervals that will be decided.
YES! This is a sample report, but based on your assets can already give you a lot of value.
Your external attack surface is dynamic, evolving, and changing on an ongoing basis.
What you see in your current snapshot may not be relevant in 24 hours. Even if you have a high score now it doesn’t mean it is risk-free tomorrow
Argos currently integrates seamlessly with PANW XSOAR (for alerts consumption and updates) and Splunk (for IOC enrichment). Argos has an open API to connect to other platforms.
Our system takes the raw material from other sources, enriches it and organizes it to minimize alerts. Our system does this automatically bringing the customer precise, actionable alerts. It does not overwhelm them with multiple false alerts. In addition, at Cyberint, our analysts review the alerts so your data also gets a real human intervention to QA it in real-time and add insights where needed.

Cyberint helps us monitor thousands of events per second. We can rest assured that we are protected from anyone trying to penetrate our system. This information is available to us in real time so we could act upon it immediately
Ramon Jocson, EVP, BPI
